Curing University Math Trauma: A Hacker's Guide to Cryptography
Please, No Math
If you've studied anything related to tech, maybe even broader sciences, even if you've just sat in some beginner lectures, chances are pretty high you've been tortured with some university-level math. The chances are even higher that you started with groups, followed by fields.
Well, let me tell you something. Today might finally be the day you understand why. And I promise, it is way cooler than any math lecture you've heard on it.
Key Exchanges And Why We Need Them
You've probably heard all about encryptions in general, so I won't start the narrative of "Let's say you wanted to text your friend Robert in private ..", let's save ourselves that.
Still, think about the pure concept of a (cryptographic) secret: if a secret is vital, how would you share it with your friend? With 10 friends? With all visitors of your website?
Symmetric encryption for example, where the encryption and decryption happen with the same key, is really fast, but suffers from this problem of key distribution.
To communicate privately with 1000 people, you'd need 1000 unique keys.
I think you can see the logistical and security-related problems with that.
Asymmetric encryption solves this by using a key pair:
- Public Key: Shared with everyone. Used to encrypt data.
- Private Key: Kept secret. Used to decrypt data.
Anyone is now allowed to see your Public Key without issues, as they can not derive your Private Key; congrats, you've established a secure channel with anyone.. but did you?
One-Way "Mailboxes" Clutter Fast
Pure asymmetric encryption, like RSA [3], functions like a locked mailbox.
If Alice and Bob (yes, I know you know those two already) wanted to communicate:
- Alice gives Bob her Public Key (the mailbox)
- Bob puts a letter in and locks it.
- Only Alice can open it with her Private Key.
If Alice wants to reply securely, she needs Bob's Public Key. If Bob hasn't made one, or things in their environment are moving fast (like a chat app), managing thousands of these mailboxes, swapping back and forth, exchanging, is incredibly slow and heavy.
Basics of Group Theory
You've heard all of what follows in Uni, probably never cared for it, probably never understood why you were learning it in the first place. Let us now put those seemingly wasted hours to good use!
What is a Group?
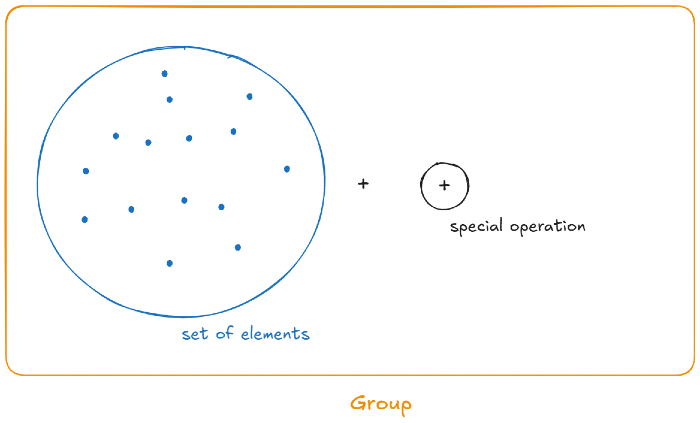
A group consists of two things:
- A set of elements
- an operation (think addition, multiplication, ...) that combines any two elements to produce a third
The collection, the "set", of items is far from random, you have strict rules the selection adheres to. The system must pass four rules, the axioms.
Group Axioms So You'll Never Forget Them Again
Let's be simple and cut the bs, shall we? As a group, I choooose $G = \{1, -1 \}$.
(This means G consists of all elements in the $\{\}$, so $1$ and $-1$).
Our operation will be standard multiplication, just like you know it: $\times$. Groups that have multiplication as their operation are called multiplicative groups.
Closure ("No Escape")
If you take any two elements from our set and multiply them together, the result must be an element that already exists in the set.
- $1 \times 1 = 1$ (inside G)
- $1 \times (-1) = -1$ (inside G)
- $-1 \times 1 = -1$ (that must be the same again as multiplication is commutative here, maybe you remember from school: $a \times b = b \times a$)
- $-1 \times (-1) = 1$ (inside G)
No matter how you use $\times$, you can't escape $G$. The system is closed.
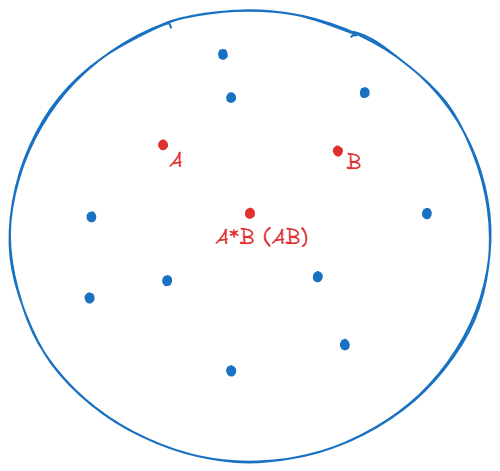
Why does crypto care about Closure?
Because if our math operations randomly produced numbers outside our defined system, computers would crash or run out of memory. We need a universe that loops infinitely but never expands.
Associativity ("Shifted Focus" changes nothing)
Btw, I am going to introduce sooome more math terms along the way so you'll recognize them when you stumble over some more exciting material. For example $\in$ literally just means "in", so if we said $1 \in G$, that's true, as we said earlier: $G = \{1, -1\}$.
When combining three or more elements, the order in which you combine them doesn't change the final outcome.
What that means formally is just that, for any elements $a, b, c \in G$:
$$
(a \times b) \times c = a \times (b \times c)
$$
Let's again test that with our group $G$:
$$
(-1 \times 1) \times (-1) = -1 \times (-1) = 1
$$
$$
-1 \times (1\times (-1)) = -1 \times (-1) = 1
$$
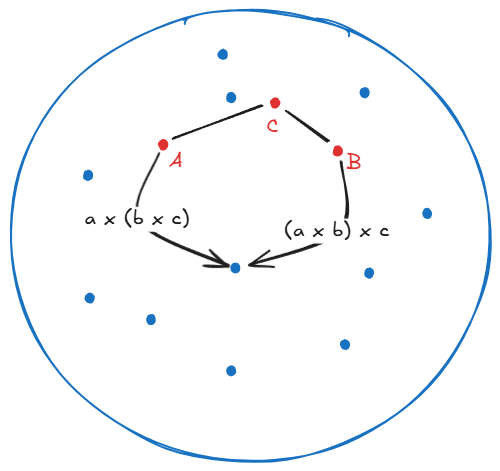
Why does crypto care about Associativity?
Because computers process massive calculations in chunks, often distributing them across different processors. If the way we grouped operations changed the final result, a multi-step encryption process would completely break down. We need a mathematical guarantee that no matter how the computer batches the calculations, the encrypted output is always perfectly consistent.
Identity Element (The "Do Nothing" Element)
Also, every group must have a "ghost" element. When you combine this element with any other item in the set, it leaves that item completely unchanged.
Let's also quickly write that formally.
CTRL + F and search for it in this post. Jump back to that explanation to remember.There exists an element $e \in G$ such that:
$$a \times e = a$$
In our set $G$, $1$ is the identity element (remember, this is called a multiplicative group):
$$-1 \times 1 = -1$$
$$1 \times 1 = 1$$
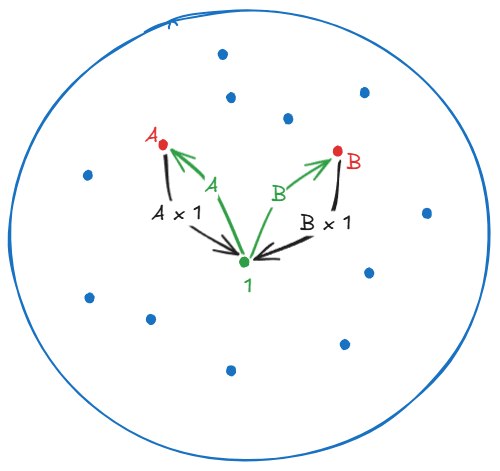
Why does crypto care about the Identity Element?
Every cryptographic system needs a verifiable baseline, a mathematical "starting line." But more importantly, without a "do nothing" element, we couldn't define the final, most crucial rule of our group: the "undo" button.
Inverse Element (The "Undo" Element)
Every action in our group you can perform must have an equal and opposite operation.
So for every element in the group, there must be a corresponding element that "undoes" its effect, returning you to the Identity Element ($1$).
Formally, for every $a \in G$, there is an inverse $a^{-1} \in G$ such that:
$$a \times a^{-1} = 1$$
In our simple group:
- What undoes $1$? Itself (not so usual, just happens to be in our group). $(1 \times 1 = 1)$
- What undoes $-1$? Again, itself, again: not that usual. $(-1 \times -1 = 1)$.
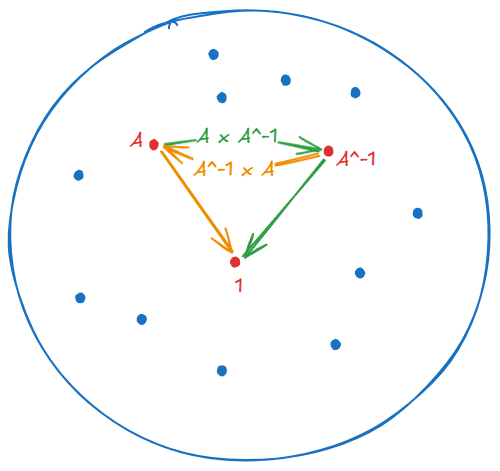
Why does crypto care about the Inverse Element?
This is the literal magic behind decryption! If you apply a mathematical operation to scramble a message (encryption), you must have a mathematical guarantee that an exact opposite action exists to unscramble it (decryption). If an element doesn't have an inverse, you can't decrypt the message. Your data would be locked and lost forever.
Mnemonics so you'll remember
Let's get creative so you don't forget these four, shall we?
Chess Associations Inspire Intelligence; remember that.
Or maybe you are a better learner with short metaphoric stories?
A group is like a magic hostel with strict rules: you can't leave (Closure), there's always someone who does nothing (Identity), everyone has an exact opposite (Inverse) and the order in which you greet people doesn't matter.
Scaling Up: Leaving the Kiddie Pool
That's it. Four rules. $\{1, -1\}$ with multiplication passes all of them, so it's officially a group. Is it the most exciting group ever? No. But you now have the exact mental model you need.
Because what happens when, instead of our adorable little two-element group, we need a group with billions of elements to secure the global internet? How do we make a massive group that still follows the "Closure" rule? If we just keep multiplying huge numbers, won't they just get infinitely larger, eventually crashing our computers?
Enter Modular Arithmetic ("Clock Math")
We solve this with something you actually use every single day: Modular Arithmetic.
Think about a standard wall clock. If it's 10:00 AM, and your friend says "let's meet in 4 hours," you don't say, "Great, see you at 14 o'clock!" You know it loops back around to 2:00 PM.
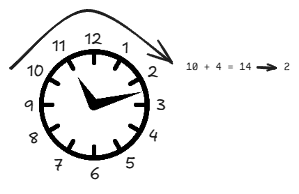
This looping mechanism is brilliant for cryptography. It guarantees Closure. No matter how many times we multiply, add, or exponentiate numbers, the result is forced to wrap back around and stay within our predefined "clock face." We've created a closed, infinite loop that never runs out of memory.
Mathematically, you just did this:
$$10 + 4 \equiv 2 \pmod{12}$$
Huh? Let's explore what that means
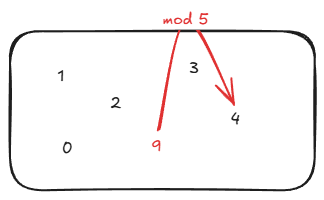
If we want to fit the number 9 onto a "clock face" that only has 5 hours on it, how do we do that? We go back to elementary school and use Euclidean division (division with remainders).
If you divide 9 by 5, it fits exactly 1 time, and you have a remainder of 4 left over. Mathematically, it looks like this:
$$9 = 1 \times 5 + 4$$
In cryptography and computer science, we care incredibly deeply about that remainder. So much so, that we use a special operator just to find it: Modulo (or mod).
If we take 9 modulo 5, we are asking, "If I divide 9 by 5, what is the remainder?"
$$9 \pmod 5 = 4$$
Why does crypto care about Modulo?
This is our ultimate "Closure" enforcer. No matter how massively huge our numbers get during encryption, the modulo operator acts like a gravitational pull, snapping the final answer back into our tiny, predictable sandbox. If our sandbox is mod 5, the only possible answers in the universe are 0, 1, 2, 3, or 4.The Ultimate Magic Trick: Modular Inverses
Now, let's connect this back to our Group Axioms, specifically the Inverse Element (the "Undo" button).
Remember that to be a group, every element needs an inverse that brings us back to the Identity Element (which is 1 in multiplication). Let's stay in our mod 5 sandbox and look at the numbers 3 and 2.
If we multiply them normally:
$$3 \times 2 = 6$$
But we are in mod 5. So, what is 6 divided by 5? It's 1, with a remainder of 1. Therefore:
$$6 \pmod 5 = 1$$
Which means we can rewrite our original equation like this:
$$3 \times 2 \equiv 1 \pmod 5$$
Read that carefully. $3$ times $2$ equals $1$. Because their product results in our Identity Element (1), 3 and 2 are inverses of each other in modulo 5.
If we want to write that out formally using the inverse notation ($a^{-1}$):
$$3^{-1} \equiv 2 \pmod 5$$
Why does crypto care about Modular Inverses?
In the real world of computers, regular division ($/$) is messy. It creates decimals and fractions, which computers hate and which break our "Closure" rule. In cryptography, we never divide. If Alice encrypts a message by multiplying it by 3, Bob decrypts it by multiplying it by 3's inverse (which is 2). This keeps all our math perfectly clean, whole, and locked safely inside our group.
The Magic of Primes & The Finite Field Sandbox
There's just one problem with our 12-hour clock. The number 12 has too many divisors ($2, 3, 4, 6$). In cryptography, divisors create predictable sub-loops. If an attacker can find a predictable pattern, they can break your encryption.
If we want true mathematical chaos, where every number mixes perfectly without getting stuck in a predictable pattern, our clock face can't be 12. It needs to be a Prime Number.
If we want to build a truly unbreakable system, our sandbox needs to be flawless:
- First, we take all the strictly positive integers from 1 up to our limit. We throw away 0 because multiplying by 0 destroys data, and 0 has no inverse.
- Second, our limit must be a massive Prime number ($p$). So our set of numbers goes from 1 to $p-1$.
Why a prime number?
As we just saw, if we used a composite number (like 10 or 12), certain numbers would share factors with the limit, and the math breaks down: they wouldn't have inverses! Using a prime number mathematically guarantees that every single number in our group has an exact, unique "undo" button.
Oh, and because it’s standard multiplication, order doesn't matter ($3 \times 2$ is the same as $2 \times 3$). When a group is commutative like this, mathematicians call it an Abelian Group, just to sound fancy.
When you take this perfect, prime-bounded group and allow it to handle both addition and multiplication flawlessly, it graduates from being a simple group. It becomes a Finite Field.
The Bridge to Real Cryptography
You did it. You survived the university math.
We now possess a Finite Field: the ultimate mathematical sandbox. It loops infinitely (thanks to Modulo), is beautifully chaotic and unpredictable (thanks to Primes), and every single element has a perfect "undo" button.
This specific structure is the absolute backbone of secure internet communication. It is the core of Finite Field Diffie-Hellman (FFDH).
In the next post, we are going to invite Alice and Bob into our Prime Number sandbox. I’ll show you the exact, mind-blowing math trick that allows them to literally yell numbers across a crowded, eavesdropped room and somehow generate a shared secret key that nobody else can possibly guess.
But to start their secret key exchange, they can't just pick any random number in the field. They need a special starting point, a mathematical spark plug called a Generator, and they are going to have to hide their secrets inside something called a Subgroup.
Grab a coffee. The real hacking starts next. No locked mailboxes required.
No spam, no sharing to third party. Only you and me.



Member discussion