research
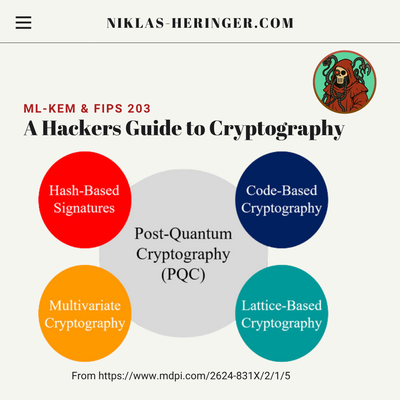
A Hacker's Guide to Post-Quantum Cryptography: ML-KEM & FIPS 203
Everything you need to understand the algorithm that's replacing RSA (in terms of Key Exchange), from polynomial rings to key encapsulation, with zero hand-waving.
skills-lab
Linux Lab Pitfalls That Will Cost You Hours
Netcat, MTU, SUID, shell stabilisation; Linux lab concepts most resources skip. Explanations, fixes, quizzes to test your depth.
privilege-escalation
Windows Privilege Escalation 02: Running through PrivEsc Paths from Zero
Working through HackTheBox's Windows Privilege Escalation module as a beginner. Every token abuse, group membership exploit, and real mistake documented. SeImpersonate, DnsAdmins, Server Operators, SeBackupPrivilege and more. No filler, just what got me SYSTEM.
privilege-escalation
Windows Privilege Escalation 01: Initial Enumeration
Hands-on walkthrough of Windows PrivEsc fundamentals, with network recon, Defender analysis, AppLocker parsing, and process enumeration. Real command output and the reasoning behind every step.
active-directory
Active Directory Pentesting: Part 02
This post covers the full GoAD setup, SMB host discovery and OSINT-based username generation to kerbrute enumeration and a first successful authentication against a GoAD domain controller. It's the groundwork every Active Directory engagement starts with.
active-directory
Active Directory Pentesting: Part 01
Before we get offensive, we get grounded. This post covers the AD fundamentals every pentester needs locked in: domains, trees, forests, the Domain Controller as crown jewel, Kerberos SSO, multi-master replication, and why even a low-privileged domain account is worth more than it looks.
digital-forensics
Digital Forensics for Beginners: How to Image a Disk, Carve Deleted Files, and Document Everything Like a Pro
Learn how to image a disk with dd, recover deleted files with Foremost and Scalpel, and document your entire investigation with forensic-log-tracker. A step-by-step beginner guide.
skills-lab
Architecting an Ultra-Minimal Linux VM with Buildroot | Part 1: Build, Break, Fix
Building the smallest bootable Linux VM that passes a professor's audit script. A hands-on walkthrough of Buildroot, from compiling a custom kernel inside Docker to debugging the four failures that broke the first boot.. and fixing them without a full rebuild.
research
Curing University Math Trauma: A Hacker's Guide to Cryptography
Remember sitting in university linear algebra, staring at the ceiling, begging the universe to tell you when you would EVER use this in the real world? Welcome. In this series, we take the seemingly useless math you slept through and show you how they secretly power the entire internet.
skills-lab
Zero to SaaS 01: Let's FINALLY understand Docker
I am reviving a failed university prototype and rebuilding it as my first SaaS. This first post strips away the mess of understanding of Docker, from the Copy-on-Write file system and layer caching to persistent volumes and container networking.
prospero
Docker CLI Cheatsheet
Now that you understand the theory of layers and volumes, here is how you actually talk to the Docker daemon. Think of this as your "Day 1" survival kit.
reverse-engineering
Learning Reverse Engineering: A Step-By-Step Series | Part 01
Dive with me into the fundamentals of reverse engineering. Learn about x86 assembly, CPU registers, the instruction pipeline, essential terms and concepts for your journey into reverse engineering.
npts
Chaos Threat Actors: Why Corporations, Parents and Legal Systems Fail against Teenage Hackers
A discussion on Joe Tidy's "Ctrl + Alt + Chaos" and my takeaways. From the release of Julius Kivimäki to the rise of "Chaos-Evil" groups, I analyze company reactions to hacks, parents navigating the digital minefields and why the legal system might need a "cartel-style" overhaul.
insecure-deserialization
A 10/10: CVE-2025-55182 haunting React and Next.js
React2Shell seems to be the Log4Shell of the JavaScript world. We break down the unsafe deserialization in React's Flight protocol, why APT groups like Earth Lamia tried to exploit it instantly, and why your audit checklist needs to check for architectural integrity. Patch immediately!
owasp
Some Welcome Changes: Dissecting the OWASP Top 10 2025
See the complete breakdown of the new OWASP Top 10 list. Why Supply Chain (A03) and Misconfiguration (A02) displaced Injection, and how the new A10 (Exceptional Conditions) category defines modern AppSec risks in Cloud and AI environments. See the Migration Cheat Sheet for Builders and Pentesters.
blackhat
Road to Black Hat London 2025: The Trends and Talks on My Radar
We celebrate the launch of the new blog layout as I prepare to attend Black Hat Europe 2025, I present my highly curated technical agenda, focusing on critical research in enterprise exploitation, macOS malware, and hardware hacking.
ctf
Securing Silver: My 2nd Place Win at CYBERSECURITY CONFERENCE 2025 CTF in Mannheim
My first comprehensive CTF experience at the CYBERSECURITY CONFERENCE 2025 in Mannheim, where my colleague and I secured 2nd place! We dive into the learning, the race, and essential tips on how to truly prepare (and thrive) in a 24-hour CTF challenge.