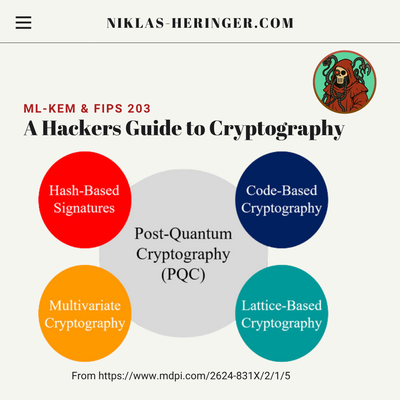
A Hacker's Guide to Post-Quantum Cryptography: ML-KEM & FIPS 203
Everything you need to understand the algorithm that's replacing RSA (in terms of Key Exchange), from polynomial rings to key encapsulation, with zero hand-waving.
Curing University Math Trauma: A Hacker's Guide to Cryptography
Remember sitting in university linear algebra, staring at the ceiling, begging the universe to tell you when you would EVER use this in the real world? Welcome. In this series, we take the seemingly useless math you slept through and show you how they secretly power the entire internet.
Road to Black Hat London 2025: The Trends and Talks on My Radar
We celebrate the launch of the new blog layout as I prepare to attend Black Hat Europe 2025, I present my highly curated technical agenda, focusing on critical research in enterprise exploitation, macOS malware, and hardware hacking.
Statistical Dreams: The Intimate History of AI
From ancient automatons to the Transformer age, this is the story of how we taught machines to think. We'll dive into breakthroughs like the Perceptron, Backpropagation, and Attention, taking a critical look at AI's origins, its dangers, and where it's headed next.
More to Go: Clean Code & Core Concepts
A hands-on walkthrough of Go’s core building blocks. Arrays, slices, loops, functions, structs, and maps - explained with performance in mind. No fluff, just clarity.
Why Go? A Hacker’s First Dive into Golang
Ever wondered why Go keeps popping up in modern toolchains and cloud-native stacks? Here’s a hands-on dive into the syntax, philosophy, and quirks of Golang; written from a hacker’s point of view.